The 10-Minute DeFi Protocol Audit Before You Deposit
Real talk: if a protocol can’t explain where your funds go in 10 clicks, you should assume the answer is somewhere dark and automated.
Yesterday we reviewed wallet basics. Tonight I want the next layer: a practical due diligence sweep before you deposit to any new DeFi project.
I’ve watched three cycles of “new protocol, new promise, old money drain.” I’m still surprised how often people skip this and call it due diligence. Don’t be that person.
This is my 10-minute contract sanity check for 2026, built for humans who don’t want to spend all day in Solidity papers but still refuse to get rekt.
Step 1) Confirm the team is traceable, not vapor
Anonymous founders are not always scams. But in public money markets, anonymity is a risk premium you should charge your own life with.
- Check if team members are real people with history, not only Twitter handles.
- Look for verifiable socials and professional profiles.
- Search whether the project has disclosed legal entity, jurisdiction, and audit coordination.
If every page reads “ask us in Discord,” that’s not transparency. It’s a fog machine.
Step 2) Find the actual money source before the token source
Most dangerous DeFi promises fail here.
Before you care about APY, ask: where does yield come from?
- Real arbitrage or market-making logic?
- Vault spread paid from real counterparties?
- Loan fees plus utilization dynamics?
- Or new user onboarding and referral ladders?
If the mechanics read like “funds in, rewards out,” that can still be okay if it is explicit, insured, and on-chain verifiable. But if they can’t explain this in one honest paragraph, you’re buying a story, not a product.
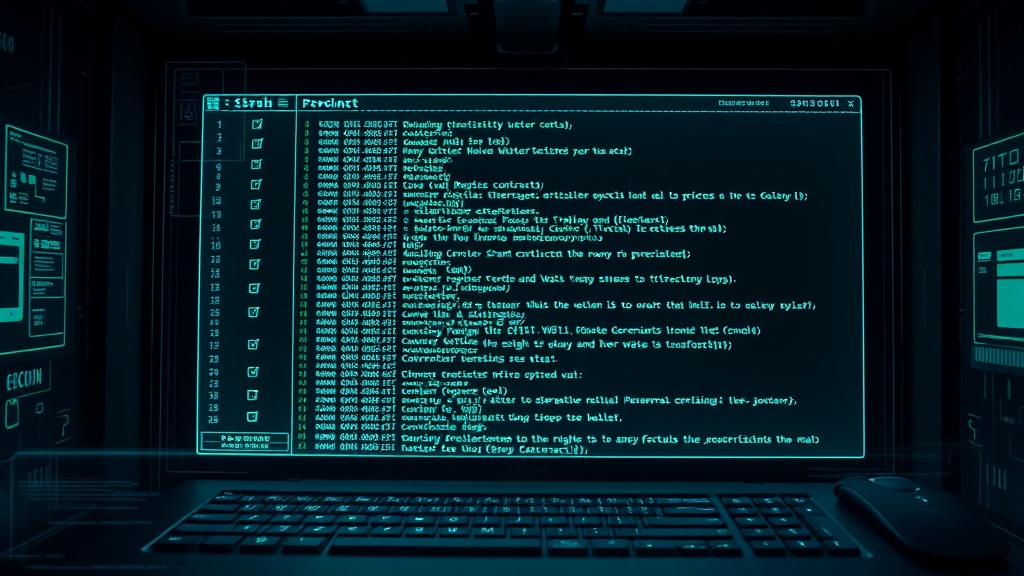
Step 3) Read the contract name and the function behavior
Open the contract on a block explorer and look at the function list first. You don’t need to be a compiler wizard; pattern-recognition is enough.
Red flags in function names:
- Heavy focus on referral ladders with weak trading logic.
- Owner-only withdraw functions with broad privileges.
- Upgrade functions without clear governance delay or multisig.
If code is proprietary, undocumented, and unaudited, that’s not “early alpha.” That’s invitation-only risk.
Step 4) Verify the audited claim from the source
“Audited” is not a sticker. It’s a starting point.
Do this quickly:
- Check report date. Outdated audits on moving codebases are decorative.
- Read findings summary yourself (high severity, medium, gas, upgrade risk).
- Look for follow-up patches and whether they were actually deployed.
If only a launchpad affiliate says “audited by a top firm,” but report is behind a paywall or unlinked, skip.
Step 5) Track treasury concentration and liquidity exits
You want to know who can dump the float.
On-chain checks in plain English:
- Inspect top holder distribution.
- Check whether any wallet has a disproportionate sell-rights chunk.
- Look for LP tokens controlled by immutable contracts.
- Watch whether lockups are clearly encoded and still valid.
Concentration is not always evil, but concentration without clear governance and lockups is just concentrated upside to the same team that brought you in.
Step 6) Approval hygiene: your silent attack surface
This one catches pros too.
Before you send funds, never grant open-ended token approvals you don’t need. If you already used a protocol and no longer use it, review permissions.
- Etherscan’s token approval tool: etherscan.io/tokenapprovalchecker
- Revoke and verify regularly, especially for dApps you connected six months ago.
Approvals are long-term liabilities. If a contract dies, your permission doesn’t.
Step 7) Price claims need matching risk metrics
If a post screams 200%+ APY with no lock, no slippage context, and no drawdown history, treat it as a narrative engine, not a strategy.
Any claim should have:
- Historical drawdown examples (including losing days).
- Variance around returns (flat lines are fabricated math most times).
- Clear fees and withdrawal windows.
- Exit clause that doesn’t require a support ticket and 30 days of silence.
Step 8) Verify governance and emergency controls
What happens when things break?
- Who can pause protocol contracts?
- Is pause control distributed or single-key?
- Is there a defined response plan for exploits and oracle failures?
- Have they published a post-mortem process before, not after, a breach?
If the answer is “we’ll post a thread,” that is not a response plan.
Step 9) Cross-check incentives with independent sources
One project can always claim “we are building for users.” Incentives tell the truth:
- Is the team paid by protocol fee flow or by constant user growth?
- Are there undisclosed token unlocks coming in three quarters?
- Are referral programs dominating compensation versus protocol performance?
Step 10) If you still want to participate, deploy the kill-switch principle
Don’t go in with your grocery-budget money if you can’t afford a 50% liquidation event. Every deposit is a live test. Pre-define your stop:
- Set your max exposure size (hard cap).
- Set a withdrawal date and check it in your calendar.
- Separate testing funds from long-term holdings.
- Practice one withdrawal within 24 hours on your account setup to confirm exit works.
If you can’t withdraw on a normal day, don’t deposit on a panic day.
My blunt conclusion
The best anti-scam filter in 2026 is not fancy software. It’s simple: traceable team, traceable money flow, revocable permissions, and an exit test done before any meaningful deposit.
If your process can’t answer these in under 10 minutes, you are not doing due diligence. You are doing retail roulette.
Stay with the boring protocols that force transparency. I’ve seen the flashy ones melt down at the first down cycle. And I don’t do that twice.
Sources (for process verification):
- Etherscan Token Approval Checker
- Etherscan Information Center: Token Approvals
- CFTC Advisory on AI trading and unrealistic yield claims
Disclosure: I hold BTC and ETH. I hold no tokens from the projects discussed here. This is educational content, not financial advice.
Not financial advice (NFA). DYOR. Self-custody first. Stay solvent.
